Enterprise TruRisk Management
Speak with our Cyber Risk Advisor for a white glove experience.
Get a tailored walkthrough of Qualys ETM based on your priorities: unified risk visibility, threat-driven prioritization, safe exploit validation, agentic AI capabilities, remediation workflows, or identity risk operations.
Unify exposures across Qualys and third-party tools
Prioritize with TruRisk™ score, business context, and threat context
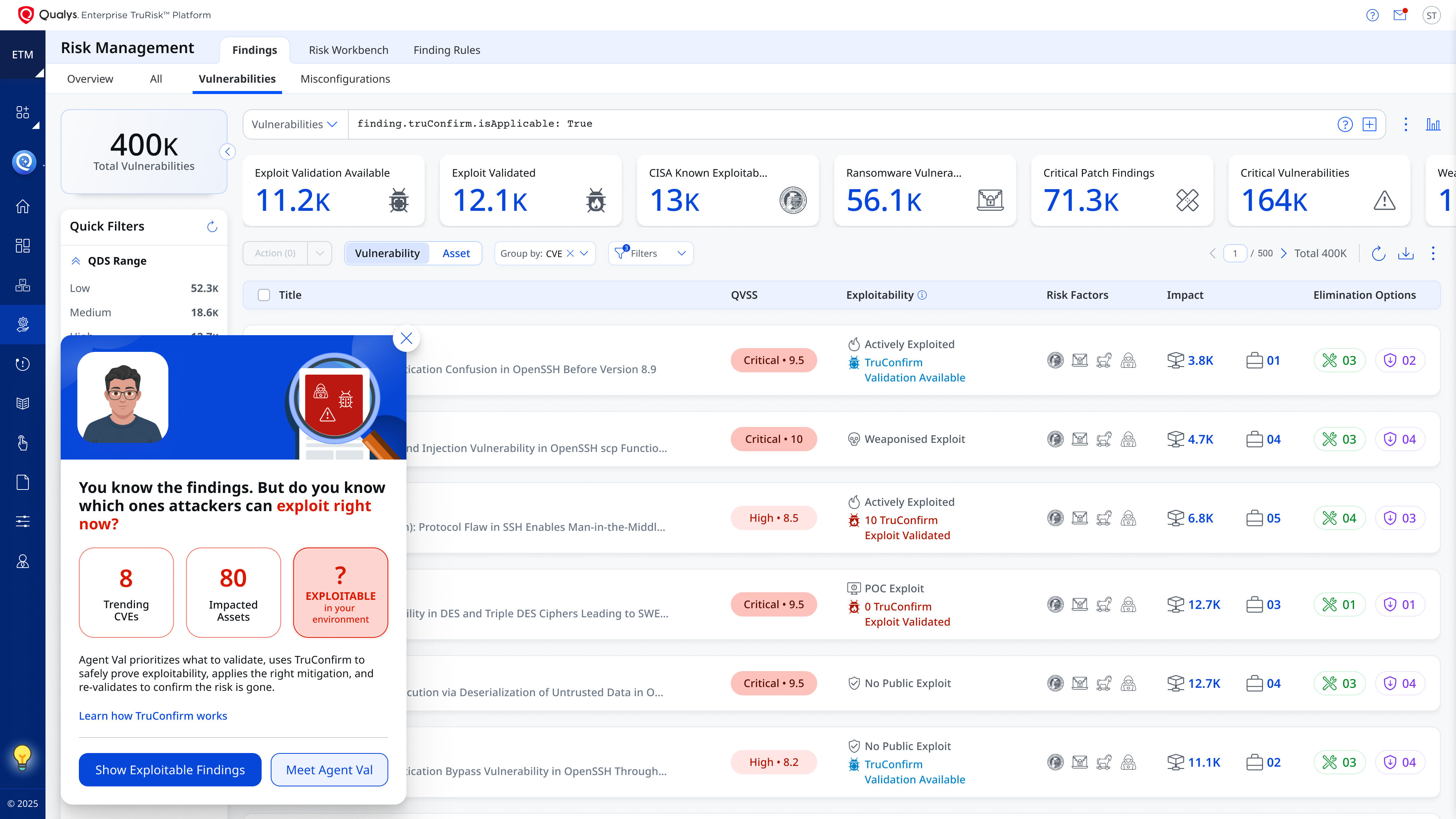
Validate exploitability safely in production with TruConfirm
Mitigate and revalidate in one closed loop using Agent Val
De-risk your business with the world's #1 cloud-based Risk Operations Center
From Fragmented tools to Unified Risk Operations
Discover how ETM scopes and aggregates findings across cloud, on-prem, containers, identities, apps, and third-party sources into one risk view.
From Threat Context to Actionable Risk
Learn how TruLens adds live threat context to exposures and TruRisk combines that with asset criticality & control signals to prioritize what actually matters.
Confirmed Exploitable Risks with TruConfirm
See how TruConfirm safely validates whether a finding is exploitable in your production environment using deterministic, production-safe validation.
Remediation and closure with Agent Val
Find out how Agent Val selects what to validate first, drives mitigation guidance, and revalidates the same exploit path to confirm closure.
Move beyond score-only prioritization with proof of exploitability in your environment.

One platform. All stages of modern risk operations with unified risk view, prioritized financial impact, and automated response across all environments.
Request Your ETM Demo. See How the Closed Loop Works.
Your session can cover TruLens, TruConfirm, Agent Val, and ETM Identity based on your priorities.
By submitting this form, you consent to Qualys' privacy policy